Configuring Cloudi-Fi
This topic describes how to integrate Cloudi-Fi with SteelConnect. It includes these sections:
Cloudi-Fi overview
Cloudi-Fi is a guest Wi-Fi provider that partners with Zscaler. Cloudi-Fi leverages and extends Zscaler for its security capabilities and performance.
The integration of Cloudi-Fi with SteelConnect provides these benefits:
•Security - Control the guest use of the network with URL filtering, content filtering, a cloud firewall, and more.
•Compliance - Store authentication and transaction logs in compliance with local regulations. Logs are also available in real time through the Cloudi-Fi administration interface.
•Customization - Personalize and brand community messages with custom format and content.
•Extended marketing - Improve the customer experience at your point of sale with fast and easy-to-use guest Wi-Fi.
As part of the Cloudi-Fi service, Cloudi-Fi support will provision a Zscaler account as an OEM service, with or without an existing Zscaler subscription. No additional infrastructure is required.
Configuring Cloudi-Fi
Before configuring Cloudi-Fi, make sure you have current Cloudi-Fi account credentials.
A SteelConnect gateway automatically connects with a Zscaler Enforcement Node (ZEN), creating a secure IPsec VPN tunnel between the Cloudi-Fi cloud and the SteelConnect gateways at sites. SteelConnect automatically chooses the best ZENs based on latency, and it enforces traffic policies configured on Cloudi-Fi. Here are some key Cloudi-Fi components:
•Each customer account is associated with one Cloudi-Fi cloud.
•Each cloud consists of ZENs in various geographic regions.
•ZENs act as proxy servers that do traffic analysis and filtering.
Automatic ZEN assignment is the default, recommended method; however, you can manually choose a primary ZEN and a secondary ZEN for each site. For example, you might need to select ZENs located in a particular country for certain geographic requirements and regulations, or for users who need to see localized content. For details, see
To manually set the ZENs for the site.
Cloudi-Fi is not supported for data center deployments using gateway SDI-5030 clusters.
Cloudi-Fi is not supported on SteelHead SD 570-SD, 770-SD, and 3070-SD appliances.
Basic steps
To deploy Cloudi-Fi and SteelConnect manually, complete these tasks:
Selecting an active cloud
The first task is to select an active cloud. The Cloudi-Fi active cloud must be different than the Zscaler active cloud. SCM warns you if you try to select the same active cloud for both Zscaler and Cloudi-Fi.
To select an active cloud
1. In SCM, choose Network Design > Cloudi-Fi.
2. Select the Account tab.
3. Specify a new domain name.
4. Specify the preshared key for the domain.
5. Click Submit.
You cannot select the same cloud for Cloudi-Fi and Zscaler. For details on Cloudi-Fi, see
Configuring Cloudi-Fi.
Cloudi-Fi active cloud
By default, SteelConnect performs automatic ZEN selection. After you select a cloud:
•SteelConnect automatically enables Cloudi-Fi and sends the list of available ZENs to all gateways.
•The ZENs belonging to the selected cloud appear.
•SteelConnect creates a Cloudi-Fi WAN for the organization.
•The gateway measures latency to all of the ZENs. SteelConnect selects the two ZENs with the lowest latency.
•SteelConnect pairs the ZENs with the sites in the organization.
•Each gateway establishes IPsec VPN tunnels to its primary and secondary ZENs through an internet connection to the assigned ZEN pairs for the sites. Automatic ZEN selection and tunnel creation finish in approximately two minutes.
•If the primary IPsec VPN tunnel or an intermediate connection goes down, all traffic is rerouted through the backup IPsec tunnel to the secondary ZEN in approximately 60 seconds. It can take up to 120 seconds.
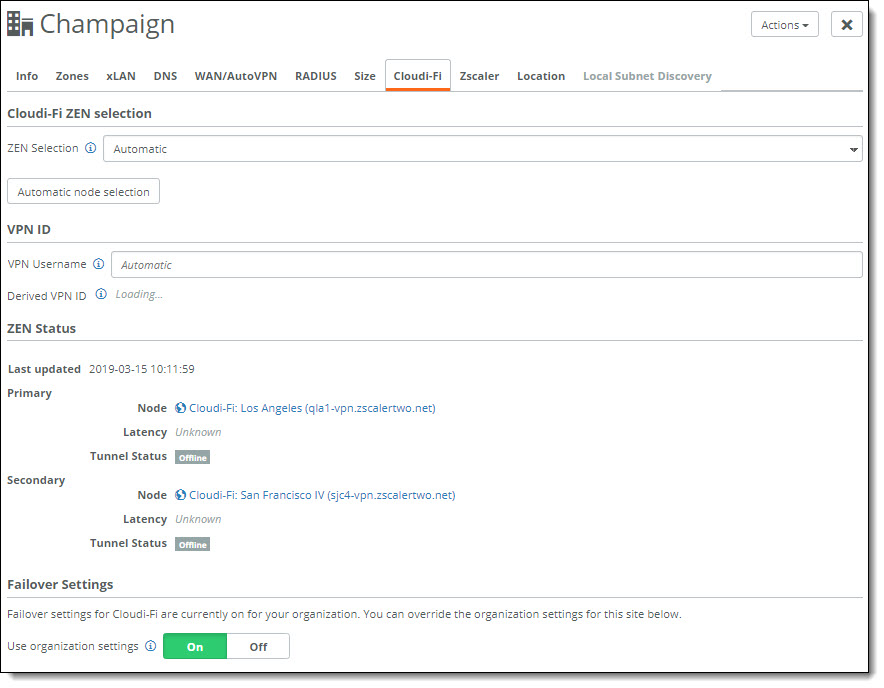
Triggering automatic ZEN selection
Because changing ZENs can briefly impact connectivity and change exit IP addresses, SteelConnect assigns the ZENs once and doesn’t update them after the initial assignment. This means that you must trigger automatic ZEN selection after you move a site to another location, change an ISP, and so on.
To trigger automatic ZEN selection
1. Choose Network Design > Sites.
2. Select a site.
3. Select the Cloudi-Fi tab.
4. Click Automatic node selection.
5. Click Confirm.
Configuring locations
A Cloudi-Fi scope provides a place to store locations in SCM.
To retrieve your Cloudi-Fi scope
1. Log in to the Cloudi-Fi administrator’s console.
2. Choose Locations.
3. Click the Scope text field.
The list of scopes to which you have access appears.
4. Locate a scope and note it for use in
Step 3 in the next procedure.
To set the scope
1. In SCM, choose Network Design > Cloudi-Fi.
2. Select the Account tab.
3. Specify the Cloudi-Fi scope that you identified in the previous procedure.
Specifying a valid scope is especially important for shared accounts so that all administrators sharing the account can manage the locations. Be careful to enter a scope you can access. If you enter a scope you don’t have access to, when you import the locations file (
Step 3 in the next procedure), the import process might create locations that you will not be able to see or manage.
4. Click Submit.
To create the locations within the scope
1. Click Download Locations.
2. Click Close.
SCM downloads the locations file in .CSV format.
3. Import the locations file into Cloudi-Fi.
Cloudi-Fi provisions the locations, which can take a few hours. The status icon in the Cloudi-Fi admin panel shows the status and lets you know when the location is ready to use.
4. After the locations are provisioned, select any of the locations you just created.
5. Click Edit Location.
6. Locate the VPN ID and the VPN key for use in the next task.
Setting the Cloudi-Fi VPN credentials
The next task is to add the credentials to SCM.
1. Choose Network Design > Cloudi-Fi.
2. Select the Account tab.
3. Specify the VPN ID domain name.
4. Specify the preshared tunnel key for the domain. The preshared key should be different than the preshared key used for Zscaler.
5. Click Submit.
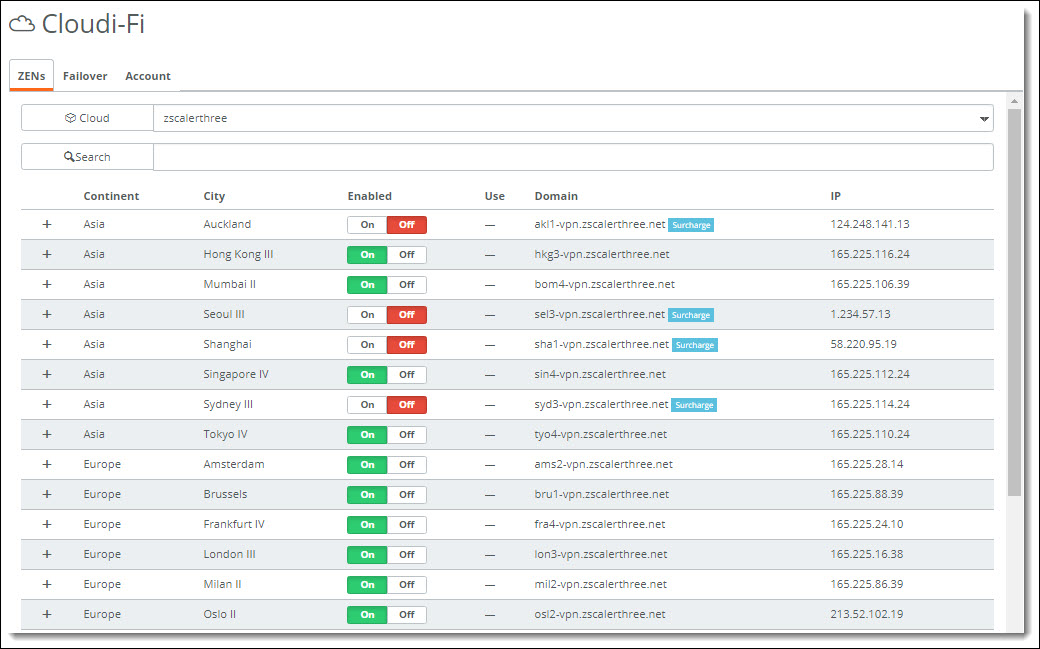
Viewing the ZEN selections
You can view the IPsec VPN tunnels ZEN selections in SCM.
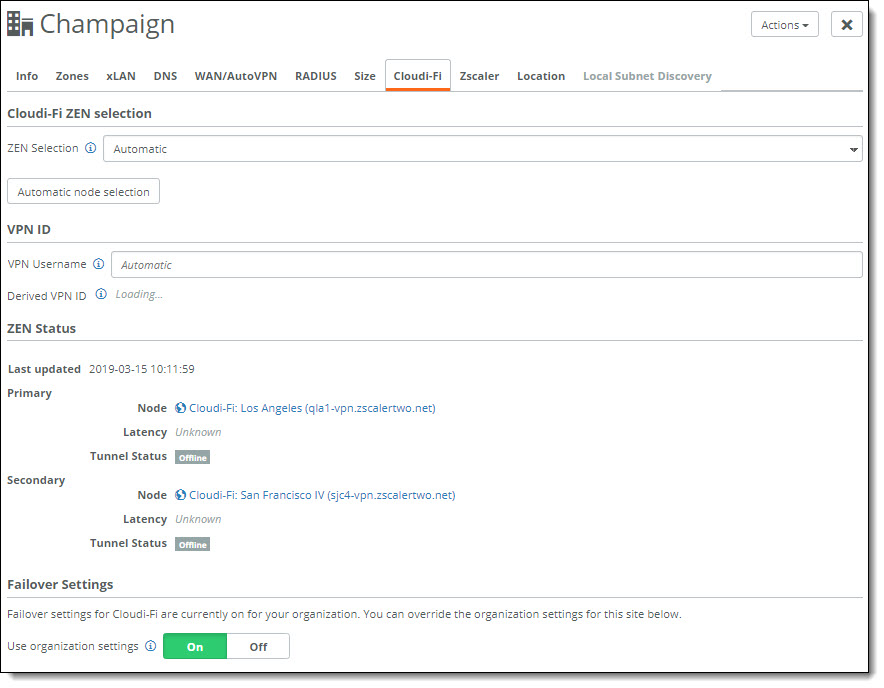
To view the ZEN selections for the site
1. In SCM, choose Network Design > Cloudi-Fi.
2. Select the site.
3. Select the Cloudi-Fi tab.
Setting the ZENs manually
Automatic ZEN assignment is the default and the recommended method; however, you can manually choose a primary ZEN and a secondary ZEN for each site.
You can use any ZEN in the same cloud. All ZENs in a cloud share the same configuration. For some ZENs, a regional surcharge might apply. SteelConnect supports ZENs with a regional surcharge.
If the automatic ZEN selections are correct, skip ahead to
Setting traffic policies.
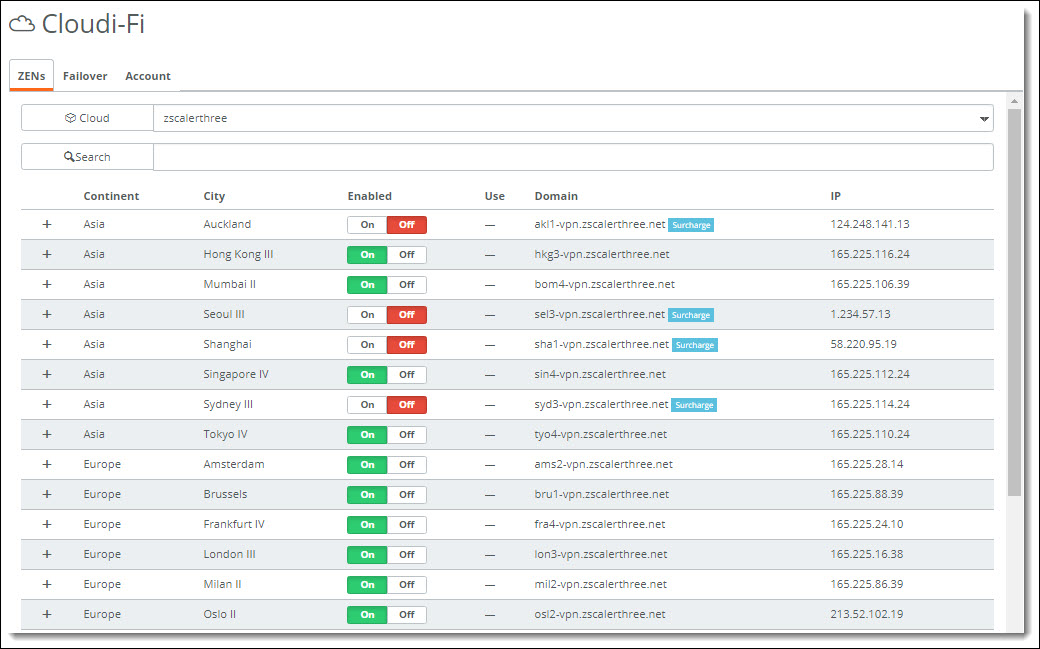
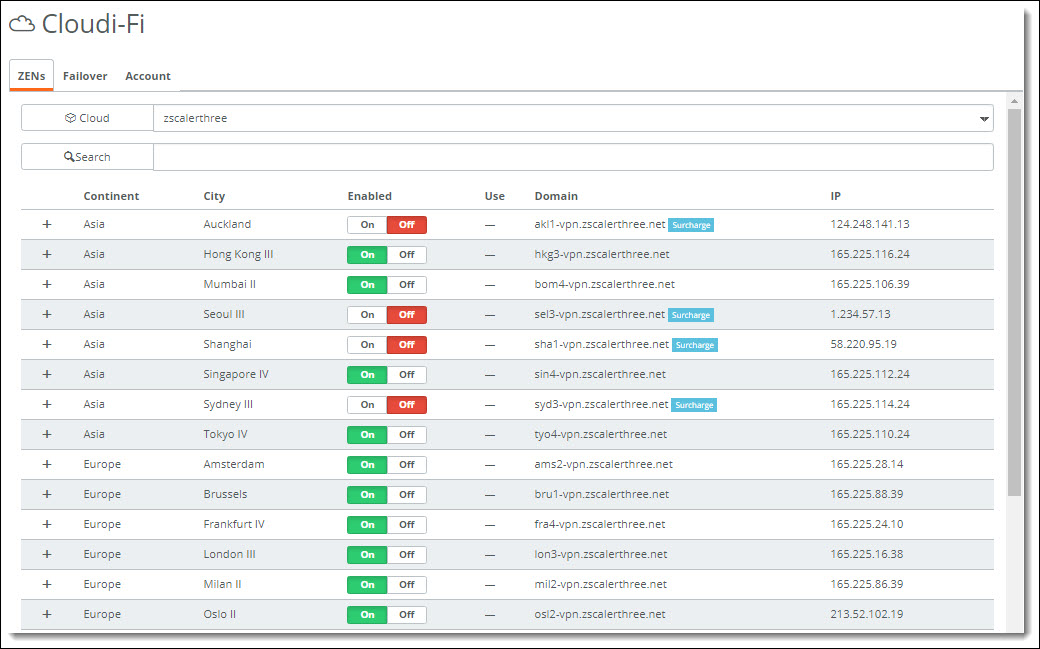
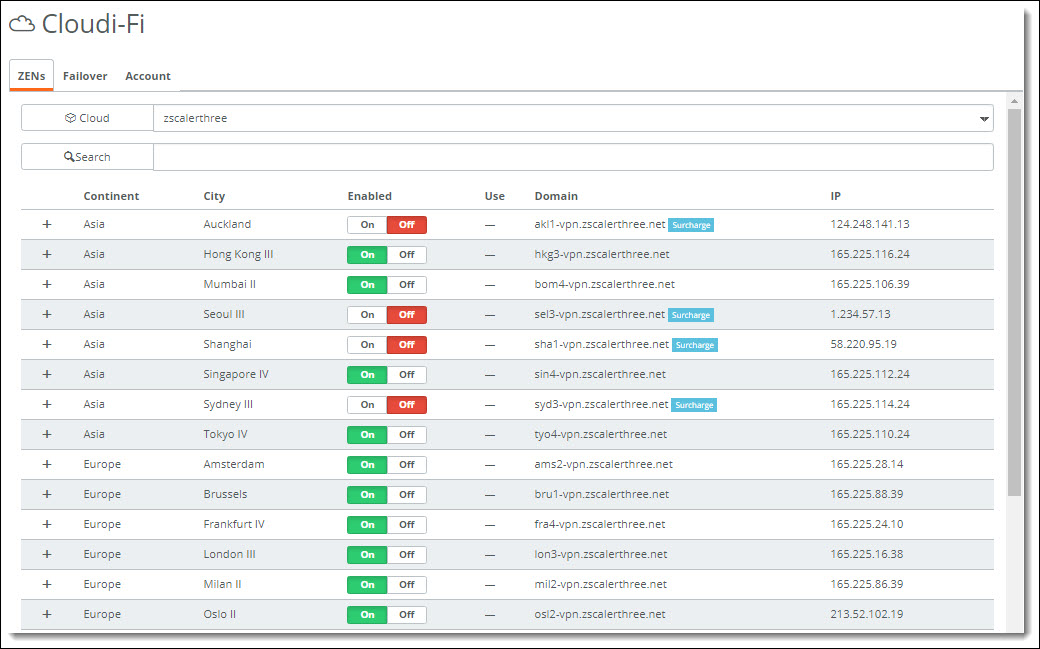
ZEN selection
To manually set the ZENs for the site
1. Choose Network Design > Sites.
2. Select a site.
3. Select the Cloudi-Fi tab.
4. After ZEN Selection, select Manual from the drop-down list.
The current primary and secondary ZEN settings appear.
5. Click the search selector and select a primary and secondary ZEN.
6. Click Submit.
SCM shows all VPN configuration details under ZEN status as soon as the system creates the third-party VPN connection. The status also reports any tunnel latency at the time of the automatic selection.
You can disable Cloudi-Fi on a per-site basis.
To enable or disable a ZEN from the active cloud
•Next to the ZEN, click On or Off.
Customizing the failover settings for an organization
SteelConnect creates IPsec VPN tunnels to the primary and secondary ZENs. The backup tunnel to the secondary ZEN is on hot-standby. Both tunnels are monitored constantly, but user traffic is only routed through one active tunnel.
SteelConnect 2.12 makes tunnel monitoring and failover faster and more reliable by using a combination of ICMP and HTTP-based monitoring by default.
You can optionally customize failover settings to adjust the methods used to monitor the primary and secondary ZEN nodes, detect failures, and switch over from primary to secondary tunnels when necessary.
The default SteelConnect Cloudi-Fi failover settings are very low-level values that work in most environments, and most values do not need fine tuning. However, if you want to adjust the settings, this section describes how. The optimal settings are balanced according to the latency and reliability of the uplinks.
Lower values shorten the failover time, but if they are too low they can create false positives. High latency sites can benefit from increasing the values, but the failover time will increase, and the failover reporting will take even longer. When in doubt, slower failover is preferred.
You can customize the failover settings for an organization, or you can customize the settings for a site.
To specify site-specific Cloudi-Fi failover settings, choose Network Design > Sites, select a site, and select the Cloudi-Fi tab. Turn off the organization settings and specify the settings for the site.
To change the default failover settings for an organization
1. In SCM, choose Network Design > Cloudi-Fi.
2. Select the Failover tab.
3. Click Off to disable the default settings. The values that were previously in use are shown as editable values.
4. Click On to enable ICMP as the method for to perform tunnel monitoring. Internet Control Message Protocol (ICMP) uses echo requests (pings) to measure round-trip packet travel times. ICMP is a low to medium overhead protocol that allows for shorter intervals and faster detection of failures (10 seconds or less). ICMP detects these failures:
–Unreachability of the Zscaler data center due to a local uplink failure.
–Something in the middle.
–The DC actually being down.
To detect other failures, enable both HTTP and ICMP.
The outbound ICMP probes travel the underlay to reach the ZENs. The uplink must allow SteelConnect to use ICMP. If you are directly connected to the internet with no firewall in the middle, your configuration already allows ICMP. If your firewall or security policy does not allow outbound ICMP, you can disable ICMP and use HTTP monitoring instead. HTTP monitoring has a high overhead and the ZEN failover time will be slower than ICMP. We strongly recommend that you allow outbound ICMP on the underlay.
5. Specify how often ICMP sends new pings, in milliseconds. If a ping fails or times out, a retry is sent immediately on the timeout irrespective of the interval. Over the period of one timeout, SteelConnect pings five times. We recommend an ICMP time-out setting of 15 seconds (15000 ms).
6. Specify how long to wait, in milliseconds, for a response before the ping and all of its retries are considered failed. We recommend an ICMP interval setting of 10 seconds (10000 ms).
7. Click On to enable the HTTP operation as an additional method with ICMP to perform tunnel monitoring, evaluation, and trending. HTTP is a medium to high overhead protocol that detects failure in 60 seconds or less. HTTP detects most failures, including:
–Unreachability of the Zscaler data center due to a local uplink failure.
–Something in the middle.
–The DC actually being down.
–A tunnel that isn’t carrying traffic.
–ZEN node failure (Layer 7, even though IPsec tunnel to the load-balance [LB] VPN might be established),
8. Specify how often HTTP sends pings, in milleseconds. If a ping fails or times out, a retry is sent immediately on the time-out irrespective of the interval.
9. Specify how long to wait, in milliseconds, for a response before the ping and all of its retries are considered failed.
10. Click Submit.
Setting traffic policies
The final task is to steer traffic through Cloudi-Fi using internet breakout preferences and/or traffic rules.
Configuring the Cloudi-Fi WAN as the internet breakout
When Cloudi-Fi is enabled, SCM creates a Cloudi-Fi WAN. You can configure a Cloudi-Fi WAN as the default internet breakout (as the organization’s default, as the site’s default, or for specific zones). For details, see
Setting the internet breakout preference and
Setting an internet breakout point for a zone.
For example, you can configure a guest Wi-Fi zone with a breakout through Cloudi-Fi.
Do not set Cloudi-Fi as the internet breakout for the zone if the organization or site that the zone belongs to has Cloudi-Fi disabled. This configuration can cause a loss of connectivity to the internet and Cloudi-Fi will be ignored. Also, if there are no other breakout options configured:
•At the organization level, traffic will be dropped.
•At the site level, SCM will fall back to the organization's internet breakout preferences.
•At the zone level, SCM will fall back to the site's internet breakout preferences.
When you select the organization's Networking Defaults tab, the site's WAN/AutoVPN tab, or the zone's WAN tab and Cloudi-Fi is not currently enabled, but has been selected previously as an internet breakout preference, a red x appears next to Cloudi-Fi in the internet breakout preference list to indicate that it is disabled.
Defining traffic rules
Configure a breakout preference to backhaul specific applications using traffic rules. Traffic rules determine which traffic is sent to the internet breakout or other VPNs. For example, you could send all traffic to the Cloudi-Fi WAN and break out internal or data center applications to backhaul them using a traffic rule. For details, see
Directing traffic using traffic rules.
Only traffic rules performing application detection based on the first packet can be used.
Do not set Cloudi-Fi as the path preference in a traffic rule for a zone if the organization or site to which that zone belongs has Cloudi-Fi disabled. This configuration can cause loss of connectivity to the internet and Cloudi-Fi will be ignored.
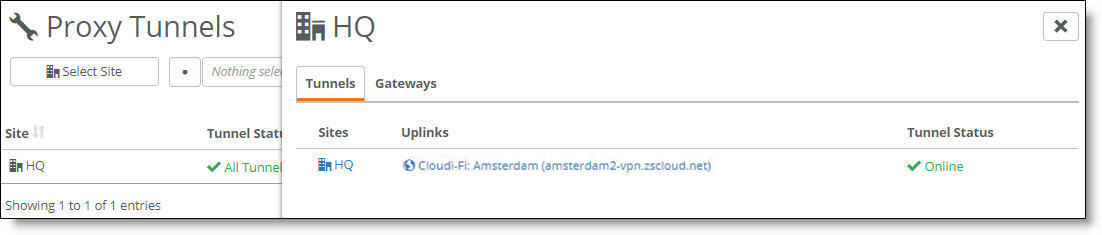
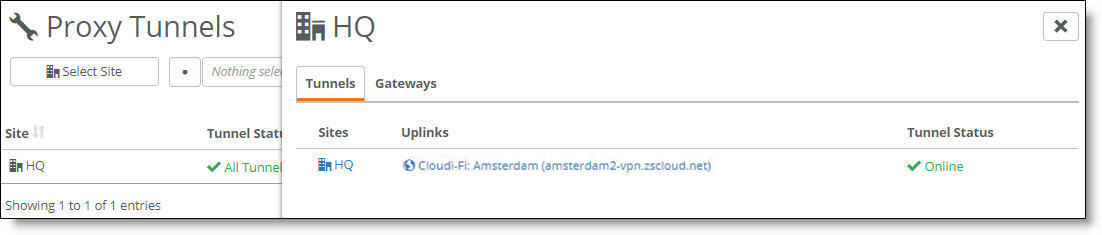
Viewing Cloudi-Fi tunnels
You can check the status of Cloudi-Fi tunnels in SCM.
The SCM dashboard shows the Cloudi-Fi VPN tunnels between sites; it doesn’t show the tunnel endpoints for Cloudi-Fi.
To view Cloudi-Fi tunnels
1. Choose Health Check > Proxy Tunnels.
2. Select a site or select all sites.
The Proxy Tunnels page shows the tunnel status for each site.
3. Click the uplink to view the ZENs in the Cloudi-Fi page.
Cloudi-Fi tunnel status in Health Check
You can also view Cloudi-Fi Analytics dashboards for reporting and analysis.
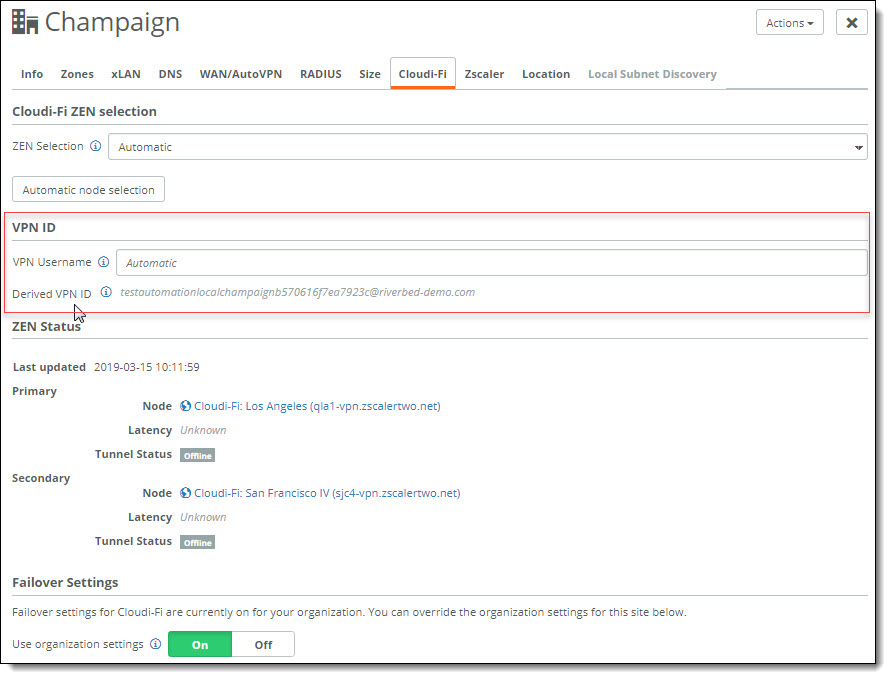
Viewing the VPN ID
You can view the VPN ID credential used for tunnel authentication in SCM. This can be useful for determining whether a site has a configured location in Cloudi-Fi.
To view the VPN ID
1. Choose Network Design > Sites.
2. Select a site.
3. Select the Cloudi-Fi tab.
The VPN username derived from the location name and the fully-derived VPN ID appears in the label below the text field.
Cloudi-Fi VPN credential for a site
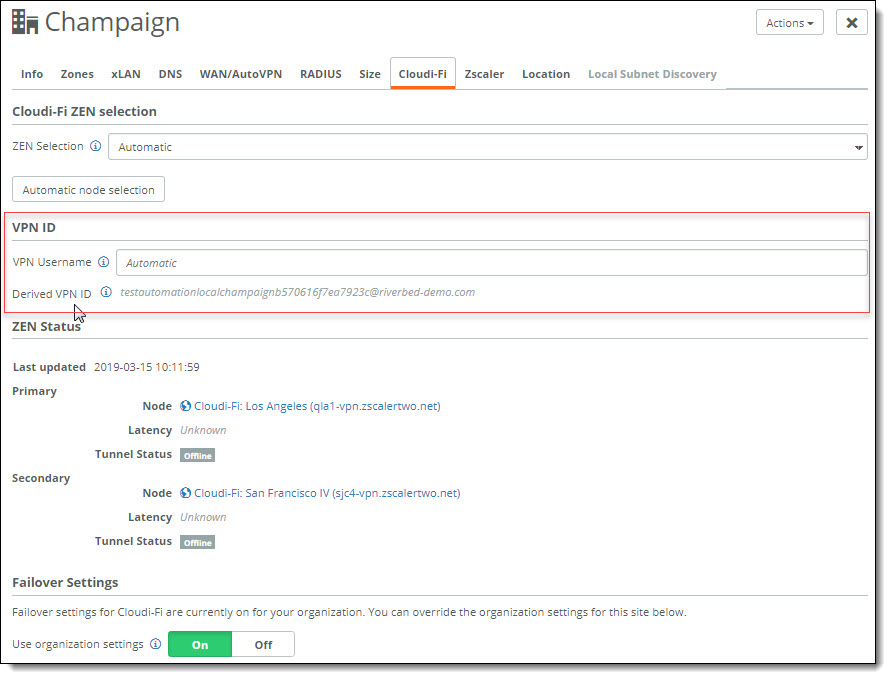
We do not recommend changing the VPN username, and typically there is no reason to do so. However, if the VPN username automatically generated by Cloudi-Fi does not match the username that SCM has generated, you can use the username text field to override the VPN username so that it matches the SCM username. Do not include a domain after the username, as SCM will add it. Changing the VPN username makes it possible to force a SteelConnect site to connect as a specific other Cloudi-Fi location.
Troubleshooting Cloudi-Fi
If a Cloudi-Fi tunnel status is offline, check these items:
•Is the configuration on Cloudi-Fi up to date? Try importing the configuration file into Cloudi-Fi again. Ensure that the VPN credentials are linked to locations and the locations have been provisioned by Cloudi-Fi.
•Could the ZEN be down? Has it moved to another location? The current list of ZENs is updated during SCM startup and reflects ZENs that were added, updated, or deleted according to their availability.
If the node is problematic, disable it in the ZEN list. Under Network Design > Cloudi-Fi, click Off to disable the problematic node. For sites with manually configured ZENs, choose a different ZEN manually.
If the Cloudi-Fi tunnels are up, but traffic is not going through Cloudi-Fi:
•Check the internet breakout configuration in the organization, site, zone, or traffic rule.
•If you’re testing a recent change, make sure that the browser is using a new connection. Changes only apply to new connections. Be aware that browsers usually attempt to reuse existing connections.
•Make sure that the traffic rules use the first packet to detect the application.
•The client must be using the SteelConnect gateway as the DNS server. This only applies to some types of traffic rules and doesn’t apply to organization, site, or zone breakout preferences.