Enabling Branch Dynamic Routing
Dynamic routing overview
To simplify integration into existing networks and provide flexible routing, SteelConnect leverages the Border Gateway Protocol (BGP) and the Open Shortest Path First (OSPF) protocol version 2.
•BGP - A Layer 4 protocol that exchanges routing information between peers to determine the optimal paths for traffic flows. Through the SteelConnect Manager (SCM), you enable SteelConnect gateways to use BGP to advertise all of their associated LAN zones (IP subnets) to an upstream router in the MPLS provider’s BGP environment. For details on zones, see
Zones within a site.
•OSPF - A Layer 3 link state protocol for routing traffic information within a single area. OSPF selects the most suitable and shortest data path for network traffic. A SteelConnect gateway in the branch learns routes dynamically from other routers in the OSPF routing domain and advertises the routes it learns. Routes specifically on the LAN-side of a SteelConnect gateway are published into the AutoVPN.
Why enable dynamic routing?
Without eBGP or OSPF, gateways use static routing to directly connect manually configured routes that access a single default route. This type of routing is suitable for small networks, but managing the static configurations becomes very time-consuming as network routing choices expand.
Benefits of dynamic routing with OSPF
Dynamic routing with OSPF on the LAN side provides reachability to multiple network prefixes over a single OSPF zone interface. All of the networks learned from an OSPF zone interface are mapped to the OSPF area that the interface is connected to.
When an OSPF-enabled uplink connects to a customer edge (CE) router, the gateway acts as a CE router to distribute routes between OSPF on the LAN side and eBGP running on the WAN side.
OSPF provides flexible subnet management as follows:
•The gateway learns local networks from the OSPF area that the zone interface is connected to.
•The gateway maps the learned networks to the zone.
•When the zone is member of a WAN, all of the networks learned from that OSFP area become routable over the WAN.
•While the peering session is up, the neighbors will send updates about a new route or the need to withdraw a previous announcement.
Benefits of dynamic routing with eBGP
eBGP provides flexible subnet management in an MPLS network in these ways:
•Instead of sending static routes, the gateway sends dynamic zone advertisements through an uplink.
•A gateway can advertise all available IPv4 and IPv6 zones (subnets) to an MPLS provider’s eBGP environment. All of the eBGP-connected sites in the MPLS become aware of the zones offered by the gateway.
•The uplink advertises a site’s local network zones (LAN and virtual IP pools) and third-party routes. Guest zones are not advertised.
•The gateway learns about remote IPv4 and IPv6 zones through eBGP from the MPLS autonomous system (AS), including both gateway-based sites and CE router-based sites.
•While the peering session is up, the neighbors will send eBGP updates from one to the other each time one of the neighbors knows about a new BGP route or needs to withdraw a previous announcement.
•The uplink can also advertise third-party redistributed zones.
CE and PE routers
Customer edge (CE) routers and provider edge (PE) routers are components in an MPLS architecture. A CE router is located on the customer premises. It provides an Ethernet interface between the customer's LAN and the provider's core network. PE routers sit at the edge of the network. CE routers connect to PE routers. SteelConnect gateways also connect to PE routers.
A SteelConnect gateway can replace a CE router to advertise and receive route announcements from the MPLS underlay.
BGP
With BGP enabled, a SteelConnect gateway establishes a TCP IPv4 control channel connection over static uplinks to a neighbor on the WAN side of an MPLS network. An established neighbor can then receive BGP updates using this peering session. The gateway shares all of the BGP routes inside its private network with its BGP neighbor. The BGP neighbor shares its BGP remote subnet routes from the IP-based virtual private network (VPN), and the gateway learns the routes.
When the BGP neighbor router in the MPLS WAN becomes aware of all LAN zones offered by the gateway, it can then learn and establish reachability to the gateway’s LAN zones. When the gateway learns all of the BGP remote subnet routes, it can then establish reachability to the remote subnets.
BGP is configured differently on a data center gateway. For details on data center dynamic routing, see
Why enable dynamic routing for a cluster?.
BGP modes
BGP can run in two modes that have different behavior when advertising routing information: eBGP and iBGP. Both modes share the same low-level protocol for exchanging routes, but external BGP (eBGP) runs between routers in different autonomous systems (ASes).
An AS is a single network or a set of networks and routers that are managed and supervised by a common network administrator (or group of administrators) on behalf of a single administrative entity, such as a business division. An AS is assigned a globally unique number that identifies the network to the world.
Internal BGP (iBGP) runs between routers in the same AS.
SCM dynamic routing uses eBGP and not iBGP.
Branch dynamic routing topologies with eBGP
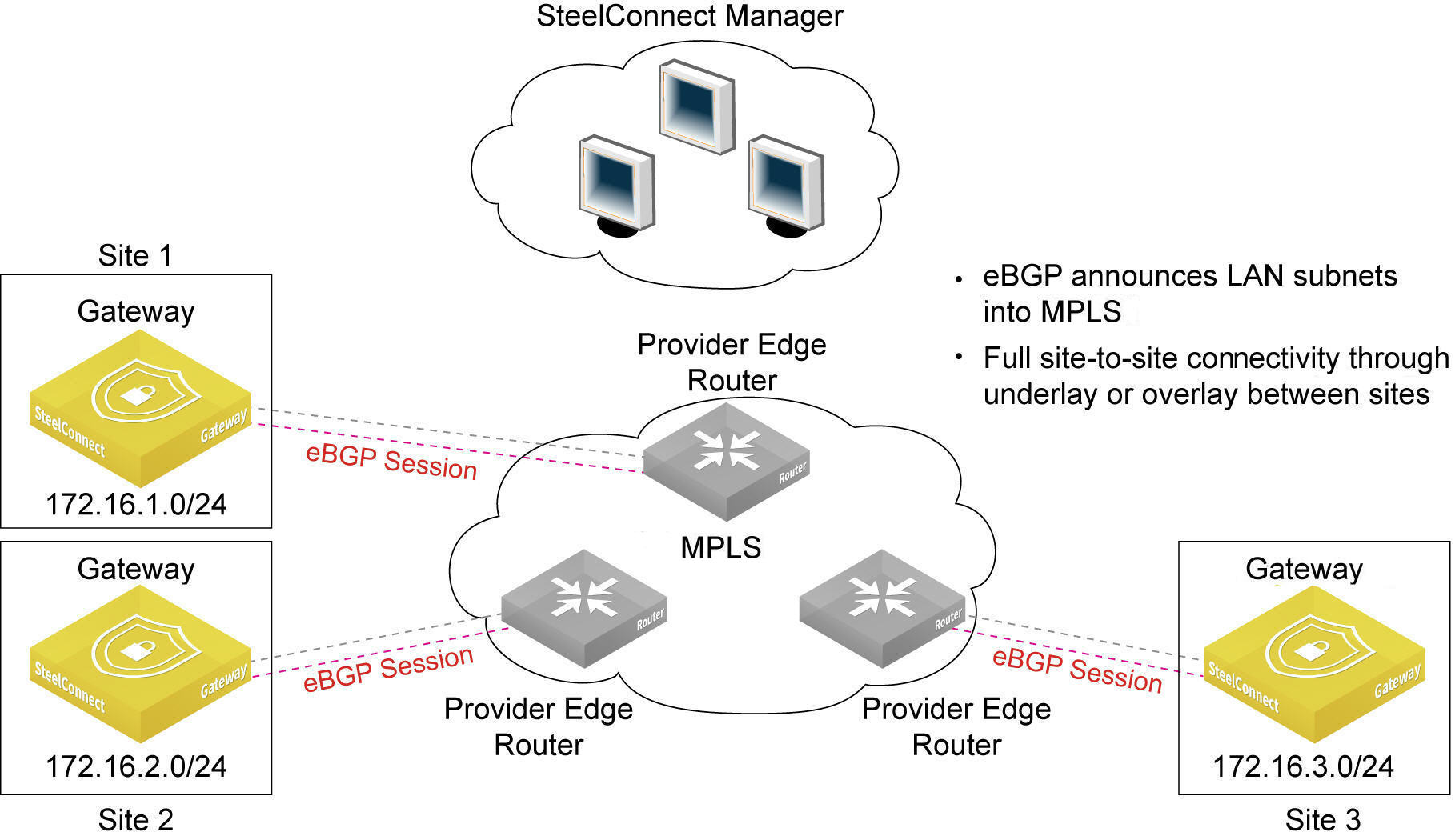
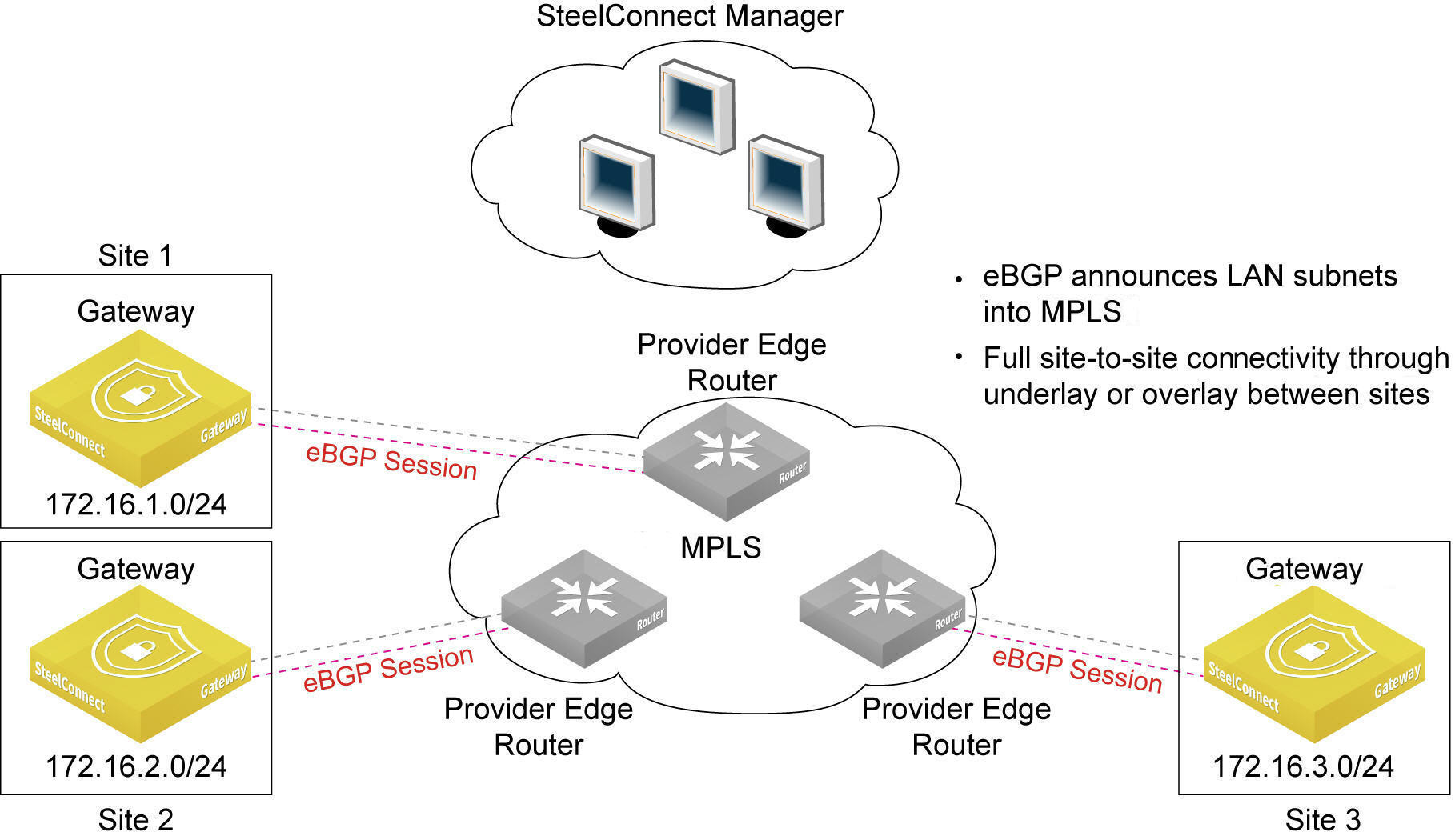
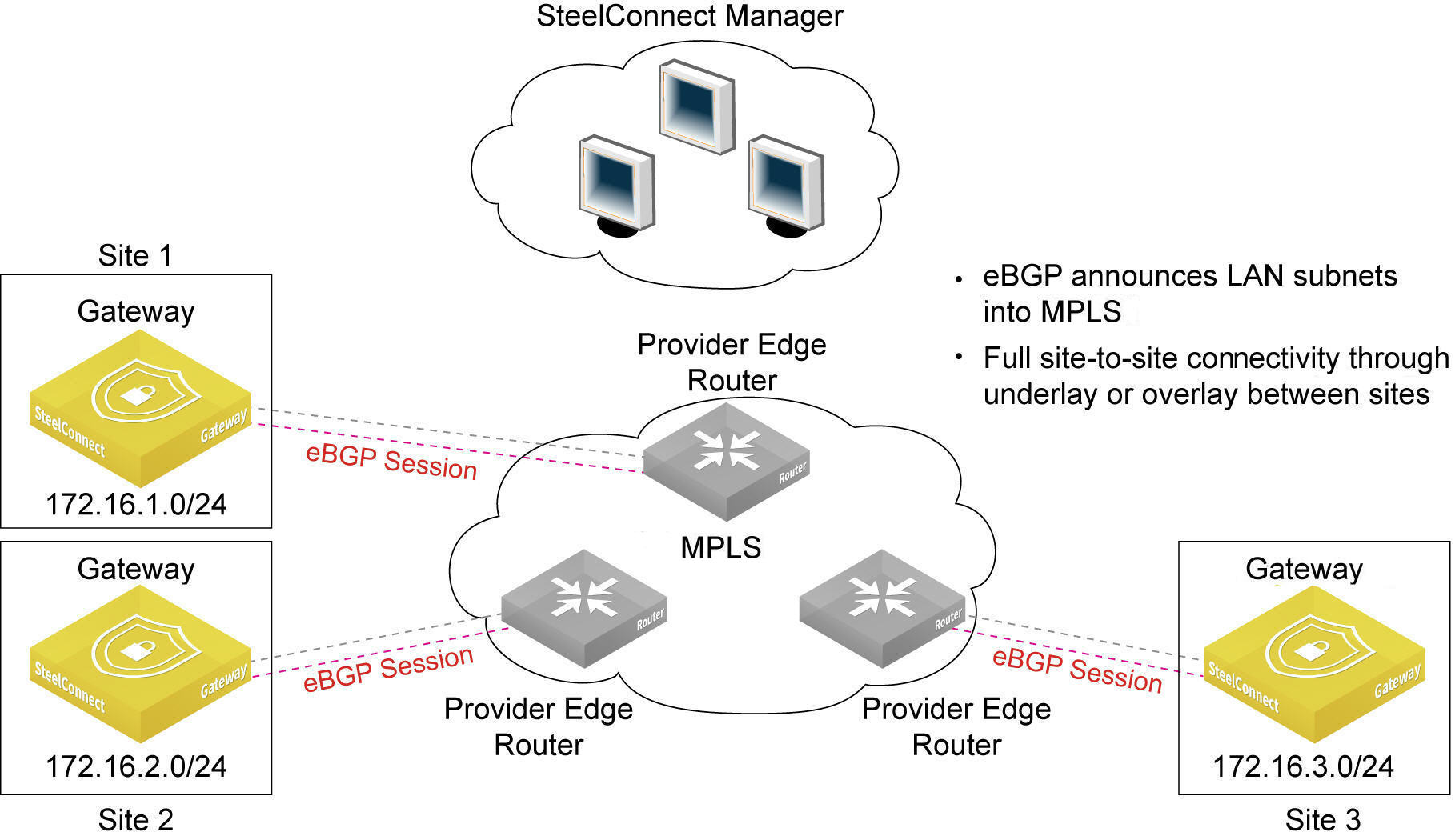
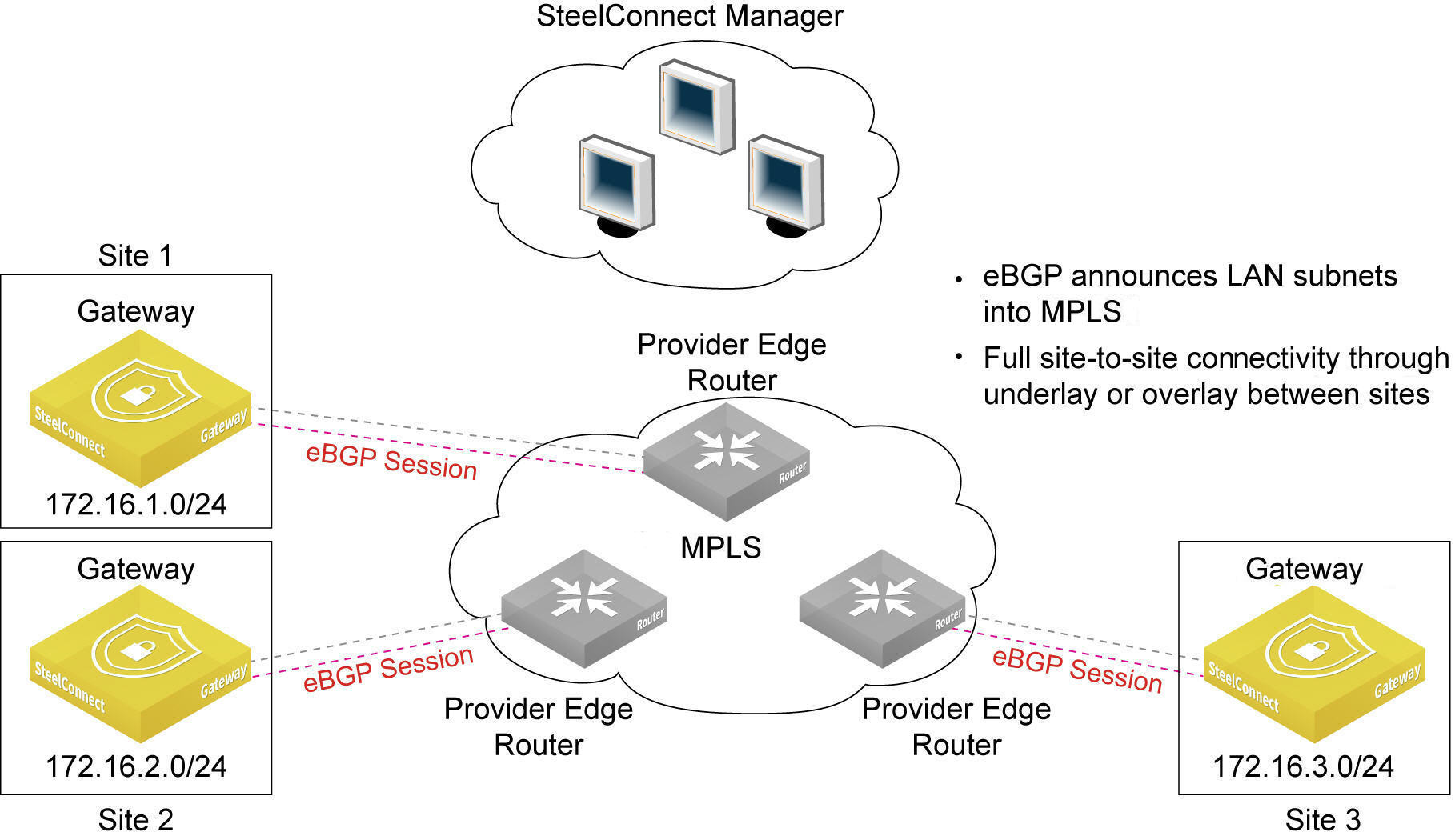
BGP supports the topology as shown in
An eBGP deployment for gateways behind intermediate PE routers. The figure shows three sites. Each site has a gateway, and each gateway is behind an intermediate provider edge (PE) router.
An eBGP deployment for gateways behind intermediate PE routers
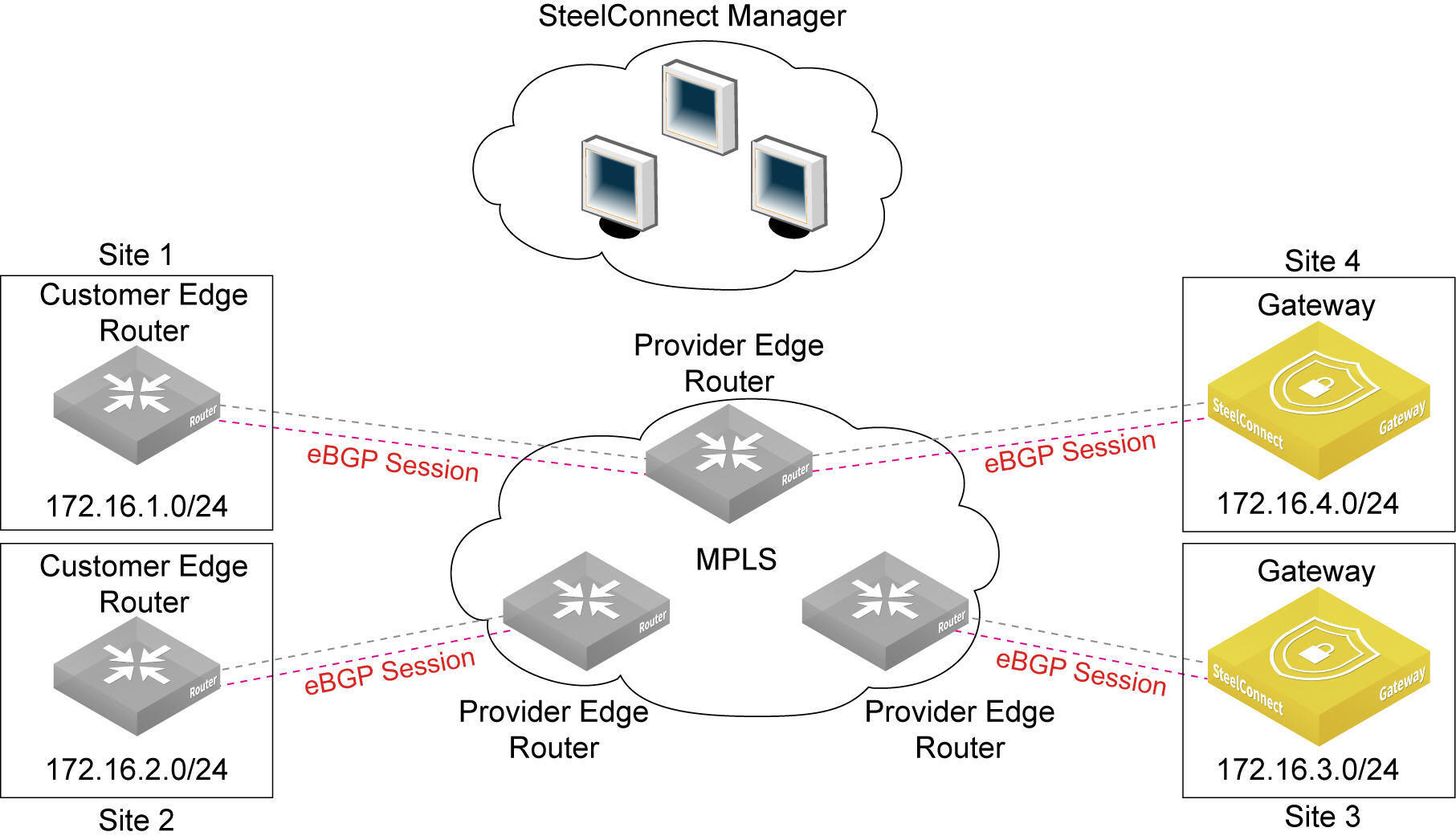
In addition to the topology shown in
An eBGP deployment for gateways behind intermediate PE routers, SteelConnect 2.1 and later support the topology shown in
An eBGP deployment in SCM 2.1 and later, which shows four sites. This deployment supports route learning from remote sites (site 1 and site 2) with subnets behind a third-party customer edge router.
An eBGP deployment in SCM 2.1
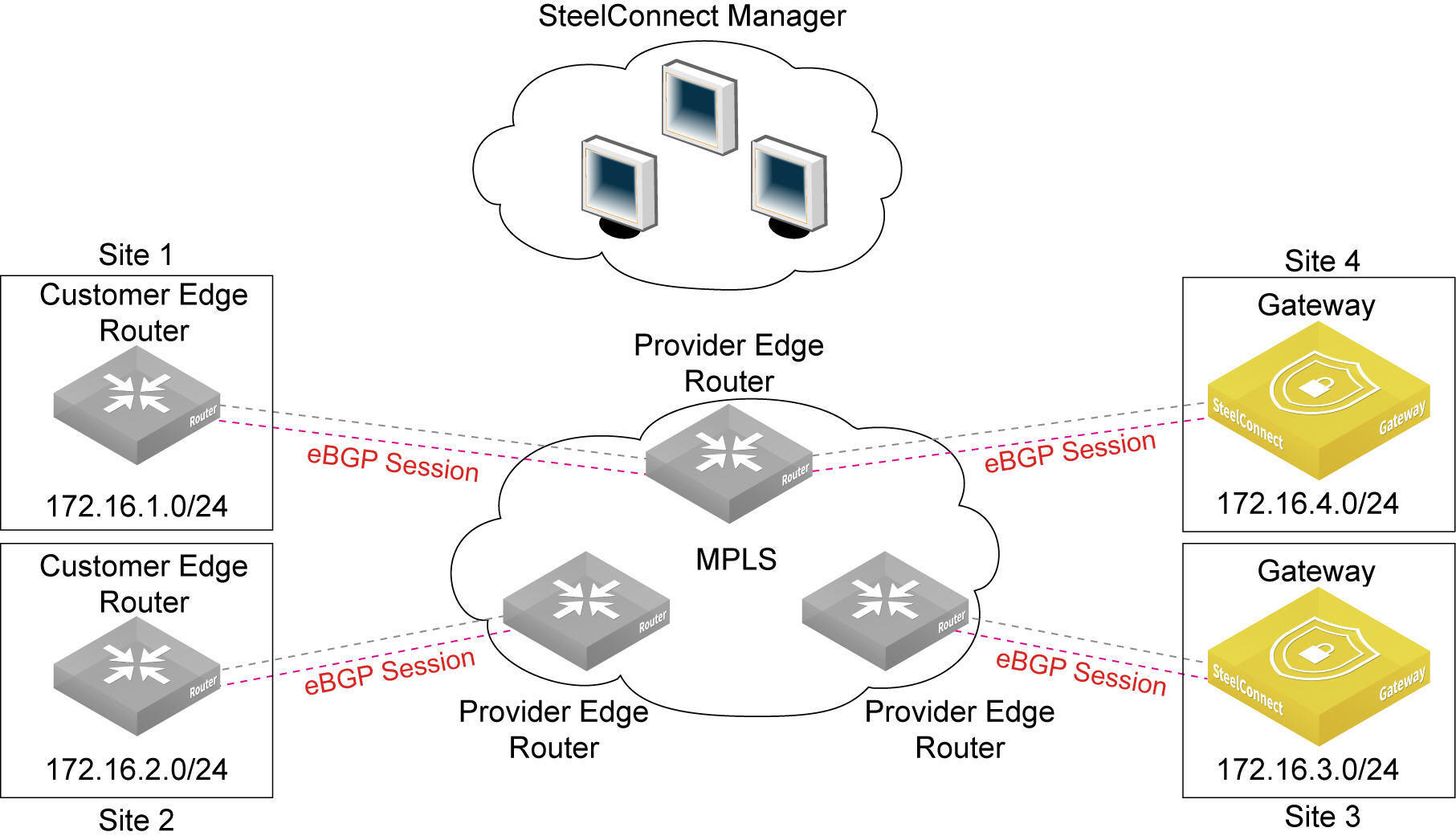
and later
New sites are connected to the MPLS through the SteelConnect gateway. The gateway uses eBGP to advertise its LAN-side subnets into the MPLS AS.
The advertised subnets are propagated to all existing CE-based sites and also to the gateway sites.
The gateway learns about remote IP subnets from the MPLS AS, including both gateway-based sites and CE-based sites.
You can enable Message Digest 5 (MD5) authentication between two eBGP neighbors to have SteelConnect verify each segment sent on the TCP connection between the neighbors.
Communication between gateways, sites, and routers
•The gateway sites communicate through the underlay or overlay.
•The CE router-based sites communicate with each other through the MPLS underlay only.
•The CE router-based sites communicate with the gateway sites through the MPLS underlay only.
•A CE router communicates with another CE router through the MPLS underlay only.
The maximum number of learned and advertised routes is 3000 across all gateway models. If the number of prefixes advertised by the PE exceeds 3000, SteelConnect brings down the eBGP peer connection with the PE. After the connection is disabled, you must disable and subsequently reenable the BGP uplink on the SCM side. To view the message indicating that the limit was reached, click the Events tab or select Visibility > Event log.
Enabling eBGP on static IP uplinks
To establish point-to-point connections between neighbors, you configure an eBGP session on a static IP uplink for a gateway and define its eBGP neighbor. Uplinks using DHCP don’t support eBGP.
By default, eBGP is disabled.
If BGP is already configured on an uplink you cannot configure OSPF on the same uplink. If the uplink is already attached to the OSPF area, you cannot configure BGP configuration on the uplink.
To configure BGP on an uplink
1. Choose Network Design > Uplinks and click New Uplink to create an uplink, or select an existing uplink. For a new uplink, select static IP and type the IP addresses.
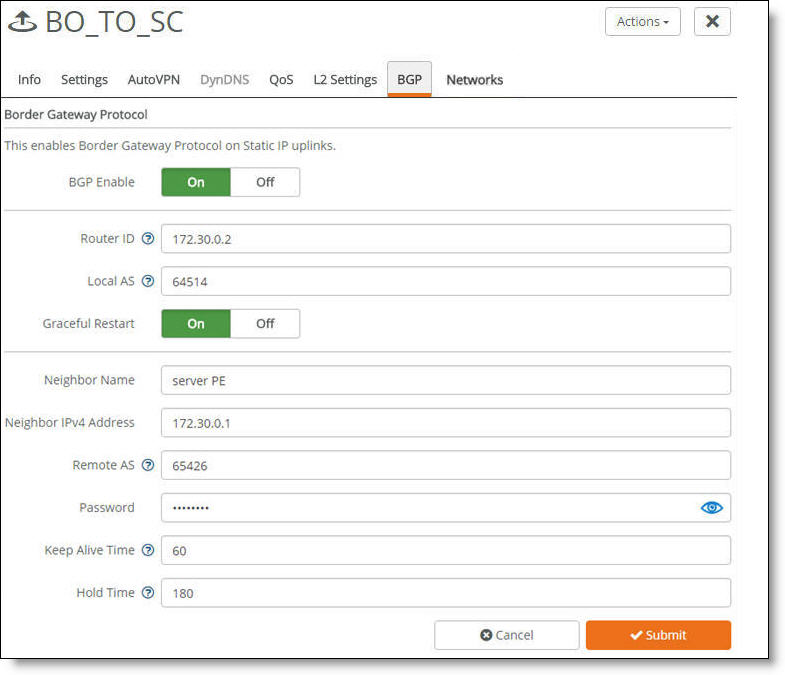
2. Select the BGP tab and click On next to BGP Enable. SCM dims the On button for DHCP client uplinks because eBGP is only available for static IP uplinks.
Enabling dynamic routing on a gateway uplink
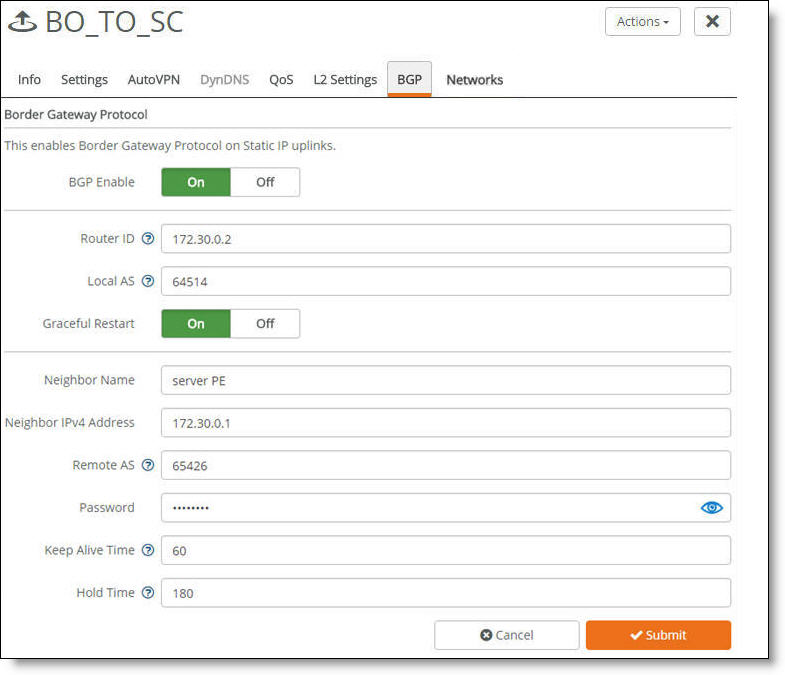
3. Fill out these required session attributes:
•Router ID - Specify the router IPv4 or IPv6 address to uniquely identify the router in the local autonomous system (AS). The gateway can peer with any remote router that supports eBGP. eBGP must be enabled on the router. If another uplink is configured with a router ID on the same appliance, SCM defaults to the same router ID used on the previously configured uplink and you can’t change the setting. You must restart SCM after changing this setting.
•Local AS - Specify the AS number the router belongs to: for example, 100. The range is from 1 to 4294967295. If another uplink is configured with a local AS on the same appliance, SCM defaults to the same local AS setting used on the previously configured uplink and you can’t change the setting.
•Graceful Restart - Click On to minimize the negative effects on routing caused by an eBGP restart from a failed peer or a changed configuration. Graceful restart allows a router to preserve its forwarding state during an eBGP peer restart. It retains eBGP peer routes and continues to forward traffic to other peers during the restart. When all eBGP sessions are reestablished, the restarting peer can receive and process eBGP messages as usual.
When enabled, SteelConnect handles configuration changes gracefully without bringing down the existing BGP sessions, with one exception: changing the local AS for an existing BGP session. SCM tears down and replaces the existing BGP session with the new BGP session using the changed local AS.
•Neighbor Name - Specify the peer name for the provider. Each uplink can support one eBGP peer.
You must restart SCM after changing this setting.
•Neighbor IPv4 Address - Specify the peer IPv4 address.
You must restart SCM after changing this setting.
•Remote AS - Specify the autonomous system number the peer belongs to: for example, 200. The range is from 1 to 4294967295. If another uplink is configured with a remote AS on the same appliance, SCM defaults to the same remote AS setting used on the previously configured uplink and you can’t change the setting.
•Password - Type a password to enable MD5 authentication. You must use the same password on both BGP neighbors. If you don’t require MD5 authentication you can leave this field blank.
Click the eye icon to see the password as you type. The view persists until you click the eye icon again to hide the password.
You must restart SCM after changing this setting.
•Keep Alive Time - Specify the amount of time, in seconds, that the eBGP neighbors exchange keepalive messages to determine whether a link has failed or is no longer available. The neighbors exchange keepalive messages often enough so that the hold time does not expire. The default setting is 60.
You must restart SCM after changing this setting.
•Hold Time - Specify the amount of time, in seconds, that a gateway neighbor waits for an incoming keepalive, update, or notification message from a neighbor before it assumes its neighbor is down. If the gateway doesn’t receive a keepalive, update, or notification message from its neighbor within the period specified, it closes the connection and routing through that neighbor becomes unavailable.
A 0 value means that no keepalive messages are sent and the connection will never close. The hold-time range is from 0 to 65535. The default setting is 180.
The hold-time value is three times the interval at which keepalive messages are sent. Using the default values for the keepalive time of 60 and the hold time of 180, the settings work together like this: after two neighbors establish an eBGP session, 60 seconds later they’ll each send a keepalive message. When a gateway receives a keepalive message from its neighbor, that gateway’s hold time for the session will have counted down from 180 to 120, but it’s then reset to 180. This process continues every 60 seconds. However, should neighbor A lose power, then neighbor B won’t receive any keepalives. So after 180 seconds, neighbor B determines that neighbor A is down and closes the session.
You must restart SCM after changing this setting.
4. Click Submit.
5. Choose Ports, select the gateway, and add the uplink to the gateway.
6. Click Submit.
7. Repeat this process for gateways behind other routers; if you have two MPLS providers, you need to create a BGP configuration for each one.
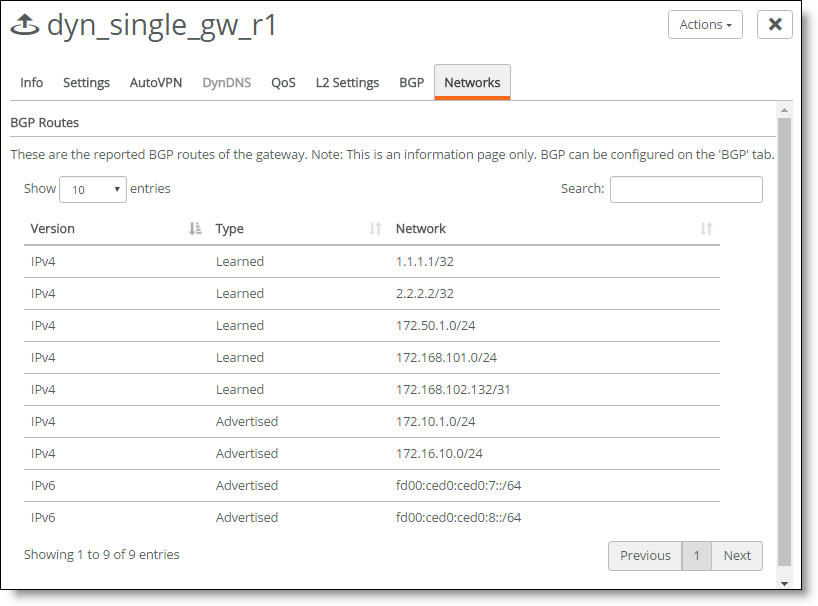
Viewing eBGP learned and advertised routes
SCM displays the advertised and learned network routes and peering session state information. To filter the list, type a search filter in the search box, for example, type IPv6 to narrow the search to all IPv6 networks.
To view eBGP network routes per gateway
1. Choose Network Design > Uplinks.
2. Select an uplink with eBGP enabled.
3. Select the Networks tab. The Networks tab is dimmed when eBGP isn’t enabled on the gateway.
The learned and advertised routes for the gateway
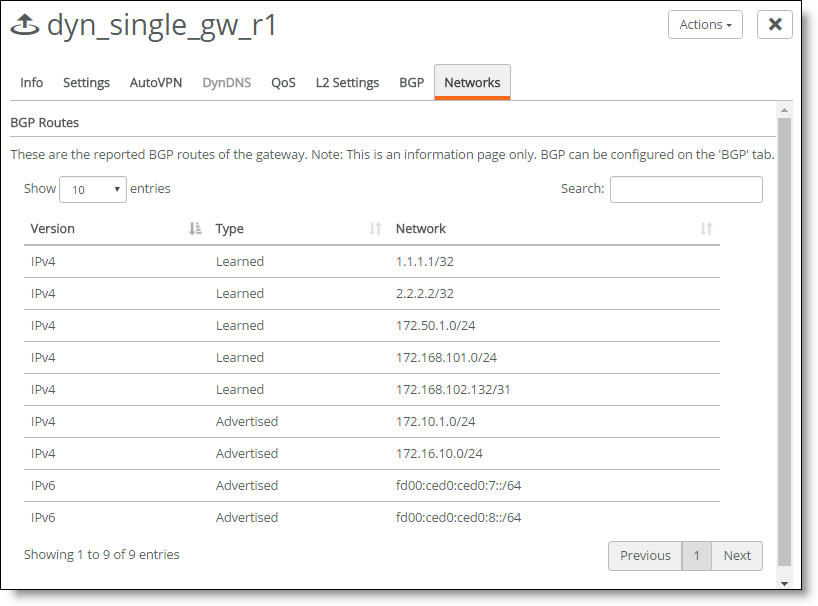
The display shows all advertised and learned network routes for the gateway, along with the route IP version number.
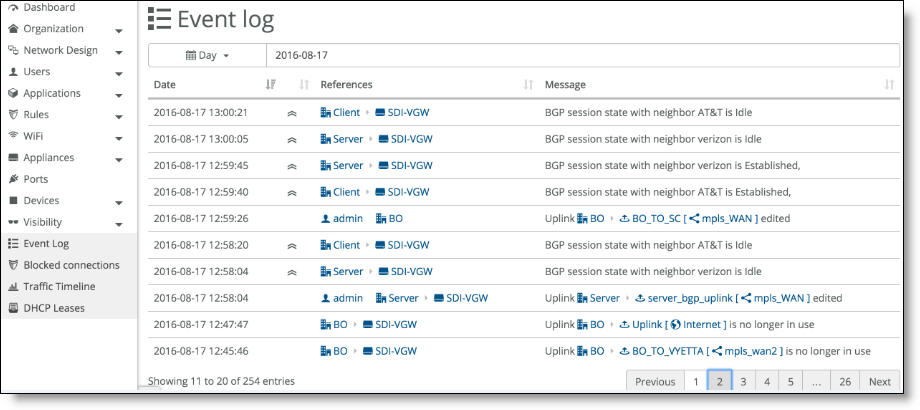
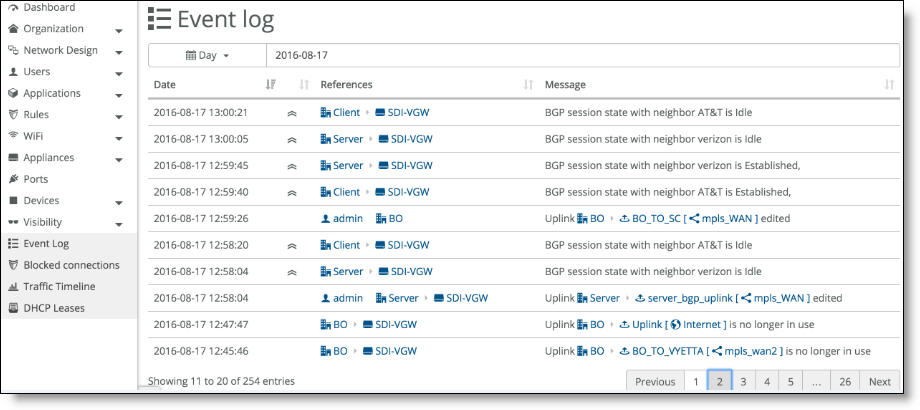
To view eBGP neighbor activity
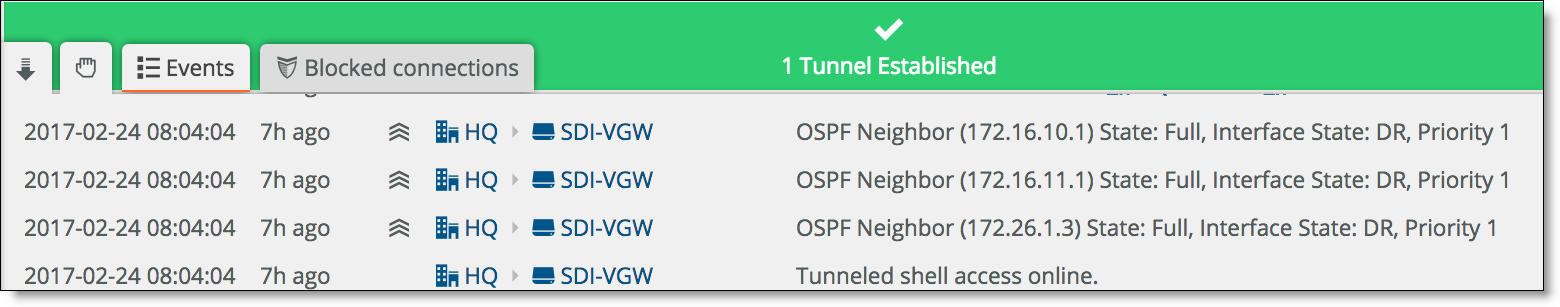
•Select the Events tab or choose Visibility > Event Log.
The event log records eBGP neighbor status
OSPF
A SteelConnect branch gateway supports OSPF version 2 in a broadcast network for dynamic routing. The gateway uses OSPF zone interfaces connected to LAN segments to learn routes dynamically from other routing devices.
In OSPF, a single AS can be divided into smaller groups called areas. An area is a set of networks and hosts within an AS that are grouped together by an administrator as a collection of IP subnetted networks.
The SteelConnect gateway on the LAN side joins an existing OSPF area in the branch network. You can also create an exclusive area.
An OSPF-enabled gateway discovers and advertises subnets in an MPLS network as follows:
•LAN-side discovered subnets are advertised on the MPLS underlay on the WAN through uplinks attached to the OSPF area. Statically configured zones are not advertised.
•WAN-side subnet discovery and advertisements work like this:
•SCM learns about subnets in a remote SD-WAN site's OSPF routing domain and configures reachability to the discovered subnets on the overlay tunnel to the remote site.
•Subnets discovered from the WAN side are advertised to the OSPF zone on the LAN side to allow reachability between subnets in the OSPF routing domain across two sites.
•The underlay connectivity between SD-WAN sites and legacy non-SD-WAN sites provides reachability between discovered subnets (assuming that both the sites have connectivity through a common MPLS WAN).
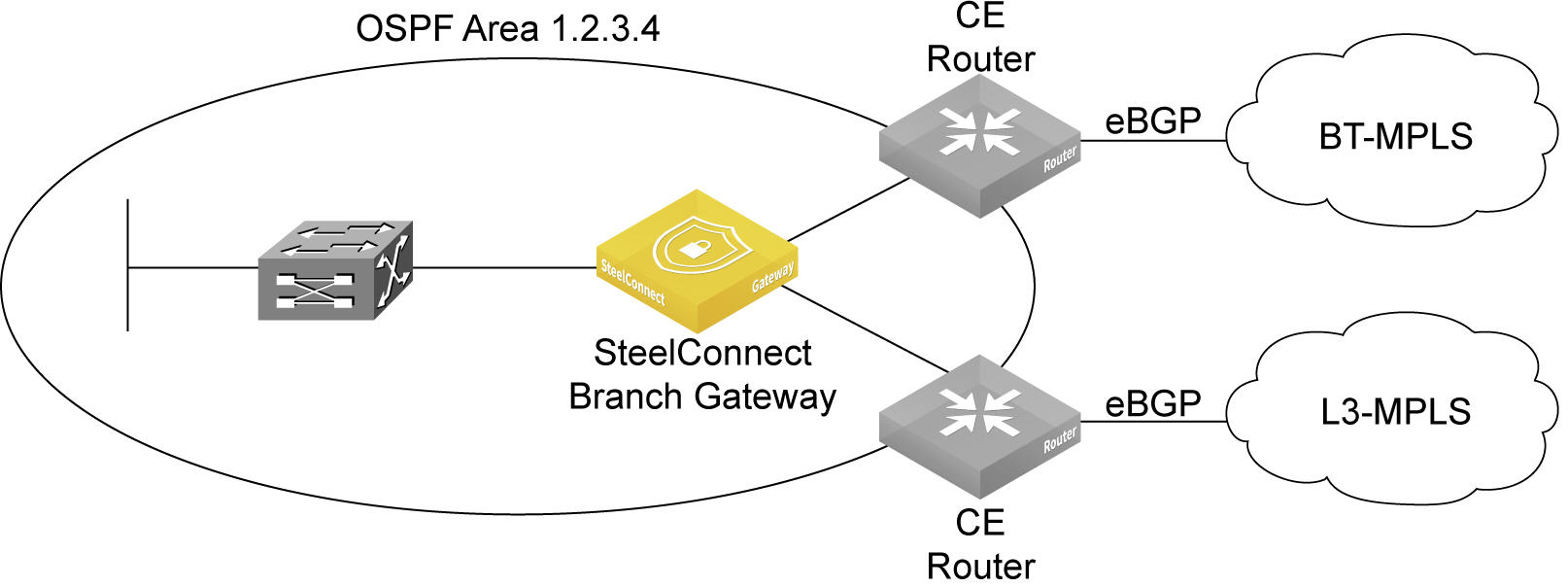
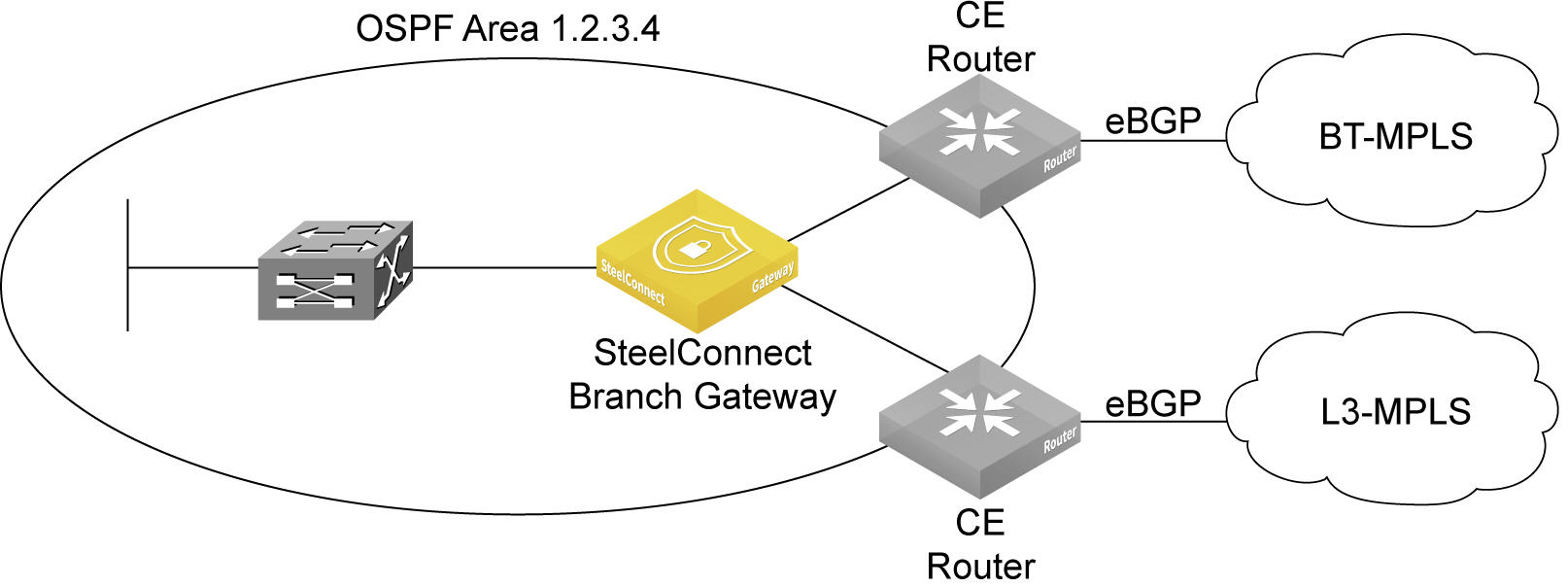
OSPF topology
SteelConnect supports OSPF for a branch site with one or two MPLS providers, where each provider is connected to a CE router. A SteelConnect branch gateway is deployed behind the CE routers. The CE routers on the MPLS WAN side are speaking eBGP and the CE routers on the LAN side are speaking OSPF. Between the CE routers and SCM on the LAN side is the OSPF domain, OSPF area 1.2.3.4 in
An OSPF area with a branch gateway.
An OSPF area with a branch gateway
Configuring OSPF routing
By default, OSPF is enabled. To configure OSPF routing on a gateway, you create an OSPF network, define a single area (or use an existing area), and attach a LAN-side zone and/or interface to the area.
Prerequisites
Before configuring OSPF on a gateway, check these requirements.
•The default gateway configuration of the zone must be set to manual mode. To set the default gateway configuration, select the gateway, select the zone, select the Gateways tab, and select Manual.
•The site where the OSPF network is located must already exist.
•OSPF must be enabled on any routing devices that will peer with the gateway.
The basic steps to enable OSPF routing are:
•Select a site and create an OSPF network for that location that includes one area.
•Attach a zone and one or more uplinks to the OSPF area.
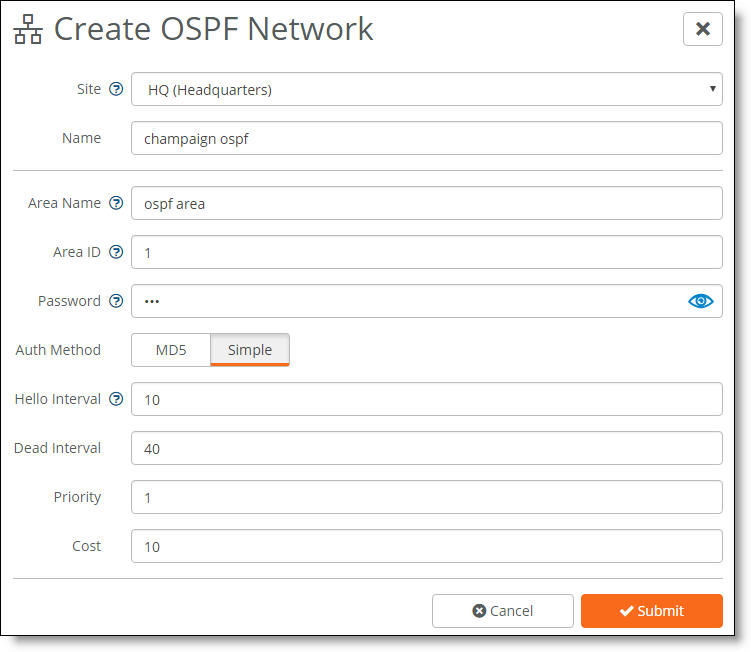
To create an OSPF network and area
1. Choose Routing.
2. Click New OSPF Network.
Creating an OSPF network on a branch gateway
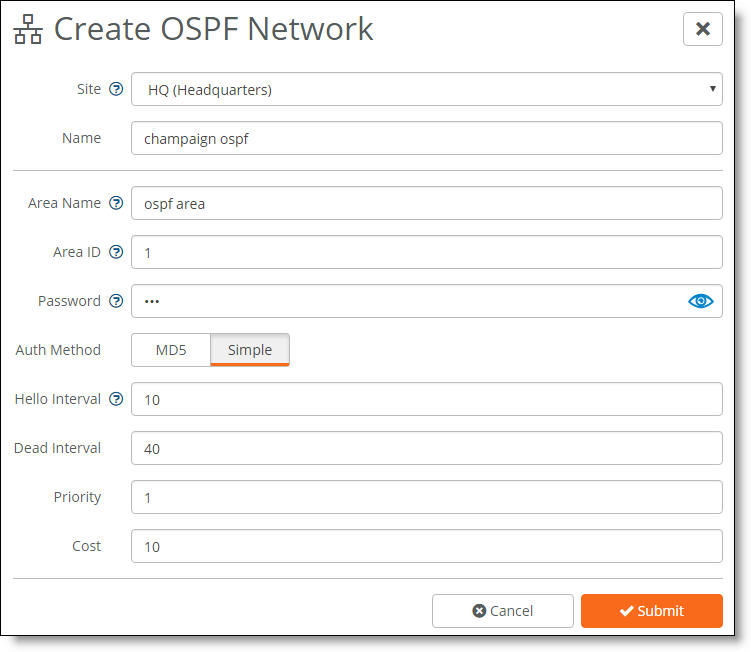
3. Fill out these network attributes:
•Site - Select the site where the OSPF network is located.
•Name - Specify a network name.
•Area Name - Specify a name for the area.
•Area ID - Specify the area in which the zone resides. Either specify a 32-bit unsigned number from 0 to 4294967295 or an IPv4 address in dotted decimal notation (x.x.x.x). The default setting is the backbone area ID 0; however, you can change the value to your existing area ID. For small LANs, area 0 might be all you need, but as a network grows, you will need more than one area connecting to area 0.
For a routing device to become an OSPF neighbor with another device, both devices must belong to the same area ID and their passwords and authentication methods must match.
•Password - Specify a password.
The authentication methods appear when typing a password. All OSPFv2 exchanges between routing devices can be authenticated using one of these methods:
–MD5 - Select this tab to use the Message Digest 5 algorithm as the authentication method. MD5 authentication enables routing devices to securely identify one another before they establish adjacency. MD5 is a cryptographic hash function with a 128-bit hash value derived from the contents of the OSPF packet and a key and key ID. This method doesn’t send the password but instead calculates and includes an encoded MD5 checksum in the transmitted packet. The receiving routing device uses the key and key ID to verify the packet.
The MD5 key doesn’t have to be the same within the area, but it must be exactly the same between two OSPF neighbors.
Tip: Click the eye icon to see the password as you type. The view persists until you click the eye icon again to hide the password.
–Simple - Select this tab to include an unencrypted plain text password with the packet. The receiving routing device uses the password to verify the packet. The simple password can be from one to eight characters and can include ASCII strings. If you include spaces, enclose the password in quotation marks. Use this authentication method when devices within an area don’t support the more secure MD5 authentication, as Simple is the least secure setting.
•MD5 Key ID - (Appears when you select MD5.) Specify a value to associate with the MD5 key. The ID is used by the receiver of the OSPF packet to determine which key to use for authentication.
To change your MD5 key, specify a new key and key ID. When both OSPF neighbors have a new key and key ID, the old key is deleted and the current MD5 key and key ID become active.
•Hello Interval - Specify how often, in seconds, to send a hello packet. Initially the gateway sends a hello packet to all OSPF-enabled interfaces to form an adjacency as a neighbor. The routing devices become neighbors and exchange link-state advertisements. After the gateway learns the common network topology, it sends the hello to check if an OSPF neighbor is alive. The range is from 1 to 65535. The default is 10. The hello interval must be exactly the same between two OSPF neighbors.
•Dead Interval - Specify how many seconds to wait for a hello packet before declaring an OSPF neighbor out of service, triggering a refresh of the link-state database and routing information. The range is from 1 to 65535. The default is 40. The dead interval must be exactly the same between two OSPF neighbors.
•Priority - Specify the priority for becoming the network’s designated routing device. The designated router originates network link advertisements on behalf of the network, and establishes adjacencies with all routing devices on the network.
The routing device that has the highest priority value on the logical IP network or subnet is elected as the designated router. A priority value of 0 means that the routing device never becomes the designated router; it doesn’t even participate in the election process. A value of 1 means that the routing device participates in the election process but has the least chance of becoming a designated router. A priority of 255 means the routing device is always the designated router.
To ensure that a routing device is elected as the designated routing device, configure the priority value to a higher value than any other interface on the Ethernet network. The range is from 0 to 255. The default value is 1.
•Cost - Specify a routing metric used in the link-state calculation. OSPF selects Ideal routes by locating destination routes with the least cost. Routes with lower total path metrics are preferred to those with higher path metrics. This setting controls the cost calculation of OSPF network segments. The default formula to calculate the cost for the OSPF metric is dividing the reference bandwidth (100 Mbps by default) by the interface bandwidth. For example, in the case of Ethernet, it is 100 Mbps / 10 Mbps = 10.
You can manipulate the cost by specifying a number within the range of 1 to 65535. 10 is the default setting.
The OSPF network needs a zone and, optionally, one or more uplinks to report OSPF learned routes to SCM.
To add a zone and uplink to an OSPF network
•Next to OSPF Interfaces, select a zone to associate with the area. Select only one zone per area for the LAN side. Only nonmanagement zones are allowed as OSPF interfaces.
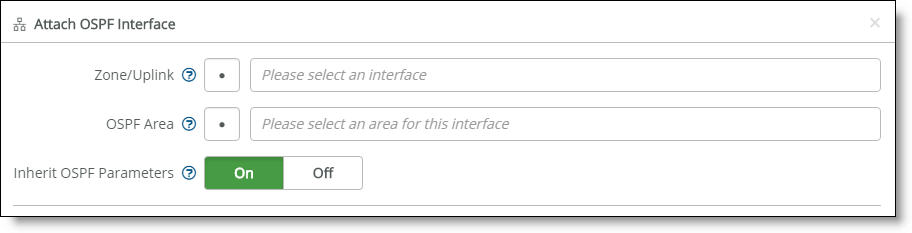
To attach an OSPF interface:
1. Select a site from the drop-down list.
2. Select the OSPF Interfaces tab.
3. Click Attach Interface.
Attaching an OSPF interface
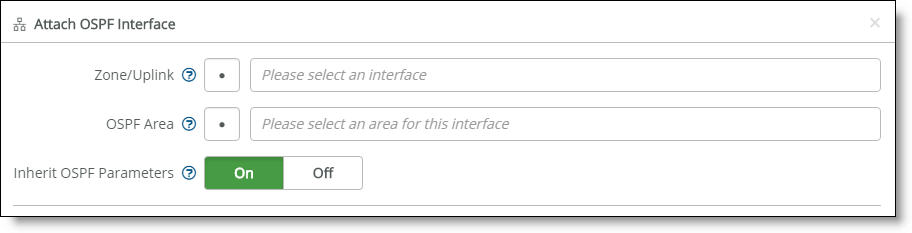
4. Fill out these interface attributes:
•Zone/Uplink - Select the interface on which to enable OSPF communication from the drop-down list.
If BGP is already configured on an uplink, you cannot configure OSPF on the same uplink. If the uplink is already attached to the OSPF area, you cannot configure BGP configuration on the uplink.
•Inherit OSPF Parameters - Click On to allow the interface to automatically inherit the area settings and any changes to an area. When enabled, making a change to the area also changes the OSPF parameters on the interface. Click Off to lock the interface configuration so any changes to the area don’t overwrite the interface parameters.
Click Off to define unique settings for the area.
5. Click Submit.
After you attach the interface to the OSPF area, the gateway configures the zone to run OSPF and establishes OSPF neighbors with LAN routers in the same network segment.
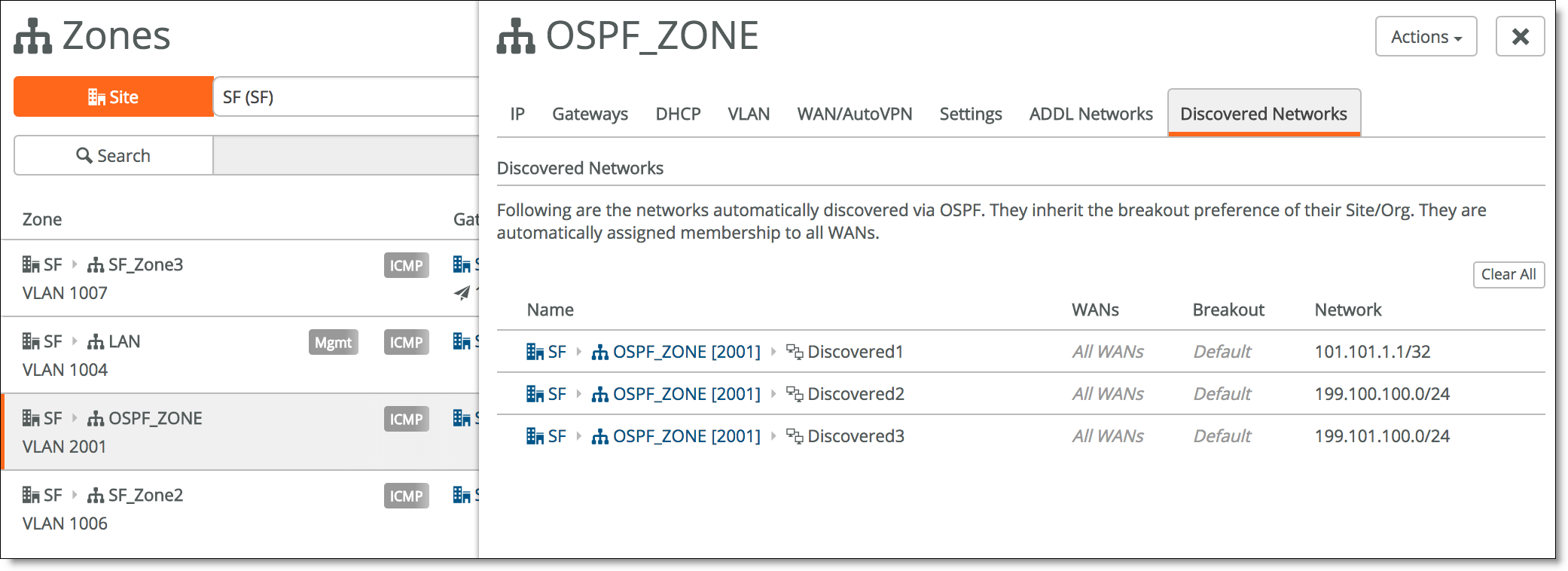
Viewing learned routes
After configuring OSPF, you can monitor learned routes in SCM. When a SteelConnect gateway is participating in an OSPF area, it discovers LAN-side subnets and reports all discovered subnets to SCM. SCM automatically configures discovered remote SD-WAN sites as reachable over the overlay tunnels.
Similarly, network subnets that are discovered on the WAN-side (primarily networks that advertise for the remote site with other SD-WAN or legacy, non-SD-WAN sites) are shown on the Networks tab associated with the uplink by which the gateway discovered those networks.
To view the learned network routes on the LAN side of the OSPF area
1. Choose Network Design > Zones.
2. Select the zone attached to the OSPF area.
3. Select the Discovered Networks tab. The Discovered Networks tab is dimmed until OSPF is enabled on the gateway.
Discovered route details
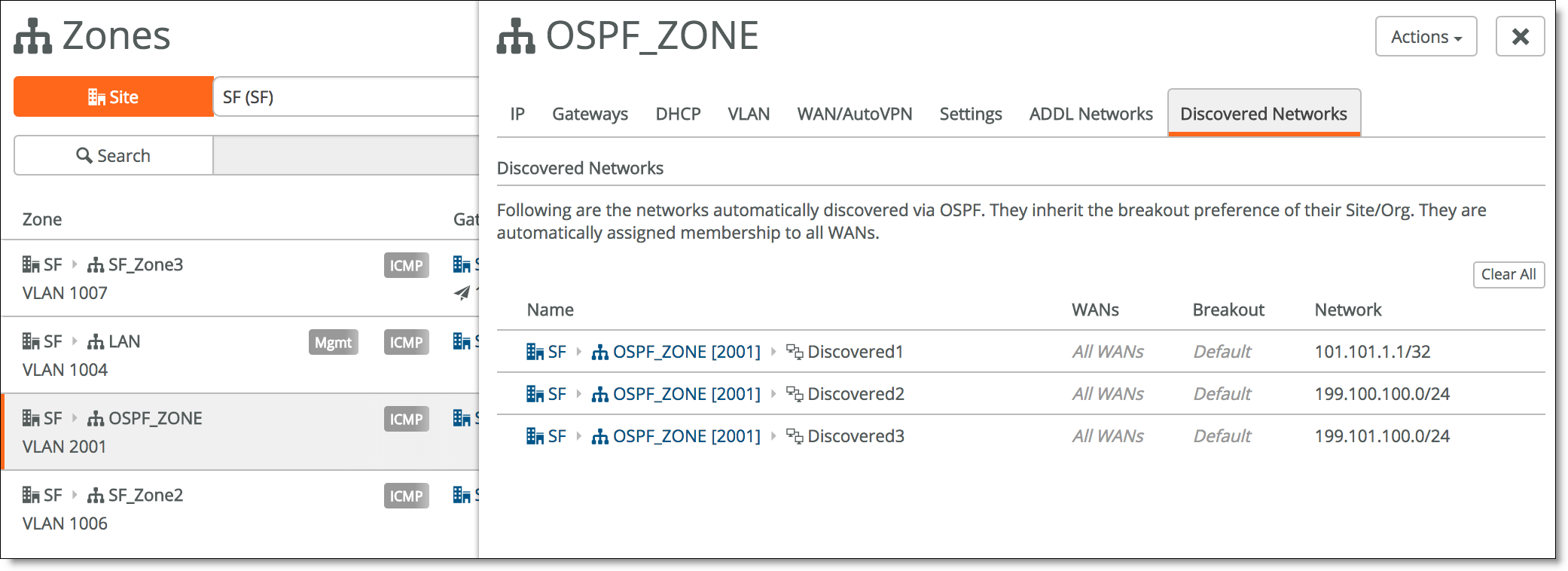
The display shows all advertised and learned network subnets for the gateway, along with the route IP version number and internet breakouts. It takes approximately 30 to 60 seconds for the discovered networks to appear.
All discovered subnets are automatically reachable on the overlay tunnel between sites.
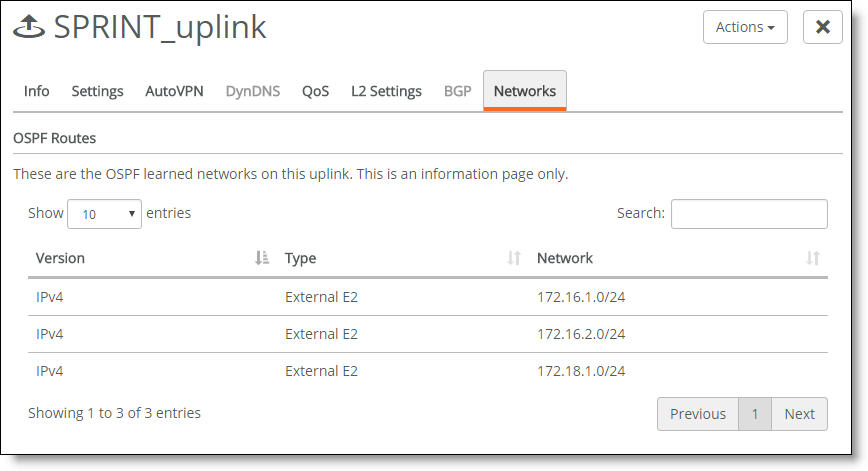
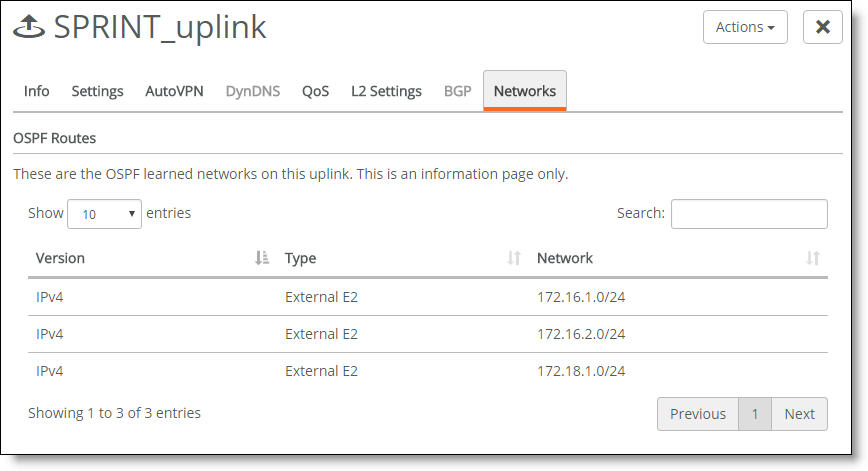
To view the learned network routes on the WAN side of the OSPF area
1. Choose Network Design > Uplinks.
2. Select the uplink attached to the OSPF area.
3. Select the Networks tab.
The WAN side learned routes
Viewing OSPF neighbor activity
After you connect a zone to an OSPF area, the gateway in the zone initiates neighbor peering with routers in that OSPF area. All neighbor peering activity appears in the event log.
To view OSPF neighbor activity
•Select the Events tab or choose Visibility > Event Log.
The event log records OSPF neighbor activity
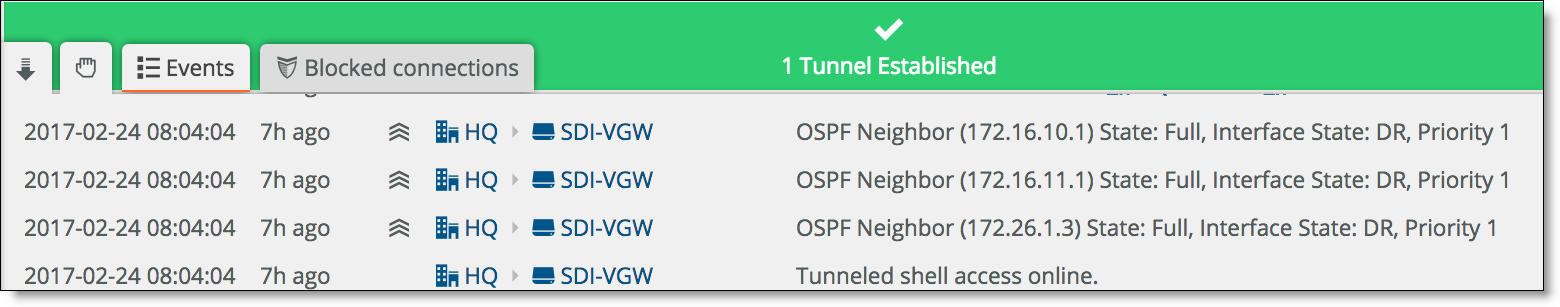
The display shows the OSPF neighbors and their IP addresses, the neighbor state, which neighbor is the designated router (DR), and the neighbor’s interface priority.
How does an OSPF zone interact with traffic rules in SCM?
When your configuration includes traffic path rules for balancing traffic or to enable security, an OSPF zone interacts with the rules as follows:
•Traffic path rule - You can create a traffic path rule for balancing traffic over multiple WANs by selecting a zone either as a source, a target, or both. The traffic path rule assigns a specific order of path preference and QoS priority to the source and target combination. When you select a static zone as the source, target, or both, the path rule applies to a specific subnet associated with the static zone. However, with a dynamic OSPF zone, the path rule provides reachability to a range of subnets learned through that OSPF zone, because the zone is associated with more than one subnet. A traffic path rule applies the specified path preference and QoS priority for the rule to all subnets learned from the OSPF zone. For details, see
Balancing traffic using traffic path rules.
•Outbound or internal rule - You can create an outbound rule that works as a filter to allow or deny traffic between a specific source and target combination. When an OSPF zone is selected as source, a target, or both for an outbound rule, the rule applies to all subnets learned from the OSPF zone.
For details, see
How do inbound and outbound rules work?. Currently, you must create an outbound rule with the OSPF zone as the source to allow TCP traffic originating from any of the OSPF discovered subnets behind the SteelConnect gateway.
 and later
and later